Top suggestions for systemExplore more searches like systemPeople interested in system also searched for |
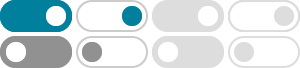
- Image size
- Color
- Type
- Layout
- People
- Date
- License
- Clear filters
- SafeSearch:
- Moderate
- Infographic About
Cyber Security - Cyber Security
Attacks - Cyber Security
Services - Cyber Security
Monitoring - Cyber Security
Magazine - Cyber Security
Risk Management - Cyber Security
Tips for Employees - Cyber Security
Expert - It Support and
Cyber Security Background - Ai and
Cyber Security - Icon for
Cyber Security - Cyber Security
Intelligence - Cyber Security
Drawing - Global
Cyber Security - Cyber Security
Strategy - Cyber Security
Lock - Industrial
Security Systems - Cyber Security
Brown - Cyber Security
Banner - Cyber Security
Model - Cyber Security
Shield Icon - How to Choose
Cyber Security Systems - Authenticity
in Cyber Security - Cyber Security
Ilasrations - Areas
in Cyber Security - Cyber Security
Specialist - Cyber Security
T - Cyber Security
Diagram - Cyber Security
Minimal - Cyber Security
Process - Cyber Security Systems
Microsift - 90s
Cyber Security - Cyber Security
Defense Systems - Information
Systems Cyber Security - Security Systems
Will Evolve - Cyber Security
Software - Cyber Security
Abstract - Cyber Security
Types - Cyber Systems
Examples - Cyber Security
Desktop Background - Cyber Security
Fundamentals - Cyber Security
FHD - Computer
Cyber Security - Cyber Security
Pciture - Cyber Security
Geeks - Cyber Security
Wallpaper 8K - Cyber Security
Vulnerability - Electronic
Security Systems - Cyber Security
Password - Military
Cyber Security
Some results have been hidden because they may be inaccessible to you.Show inaccessible results

 Feedback
Feedback